Derby, Connecticut located in the Connecticut “valley” along Route 8 was recently the scene of a ransomware attack. The Derby Police were hit with this malware which encrypts files and does not unlock them until a ransom is paid. Typically, the perpetrator is located far away – Eastern Europe or Asia and is out of reach of law enforcement in the U.S.
Organized crime syndicates and terrorist groups like ISIS are all involved in disseminating this type of malware to generate income.
Arrests and convictions for the crime of perpetrating ransomware are very very rare.
Companies quite often are forced to pay the ransom because they weren’t adequately prepared before the attack.
The challenge for these organizations is, even if they pay, they may still not get their files restored. Hackers are under no obligation to unlock files. Moroever, some variants of such attacks delete all the files on your system. In fact, the NotPetya malware variant of the Petya ransomware caused $10 billion dollars of damage just based on the reporting of publicly traded companies. The actual damage amount is likely far greater.
Another challenge is after a breach, companies could be out of compliance with regulatory agencies, state and federal laws and potentially need to report that they were breached.
In addition, after being hit, an organization’s cyberinsurance rates could skyrocket – even in they pay and get their data back.
Even worse, the data which was encrypted may have also been sent to the hacker – meaning sensitive customer information such as credit card numbers may now be for sale on the dark web.
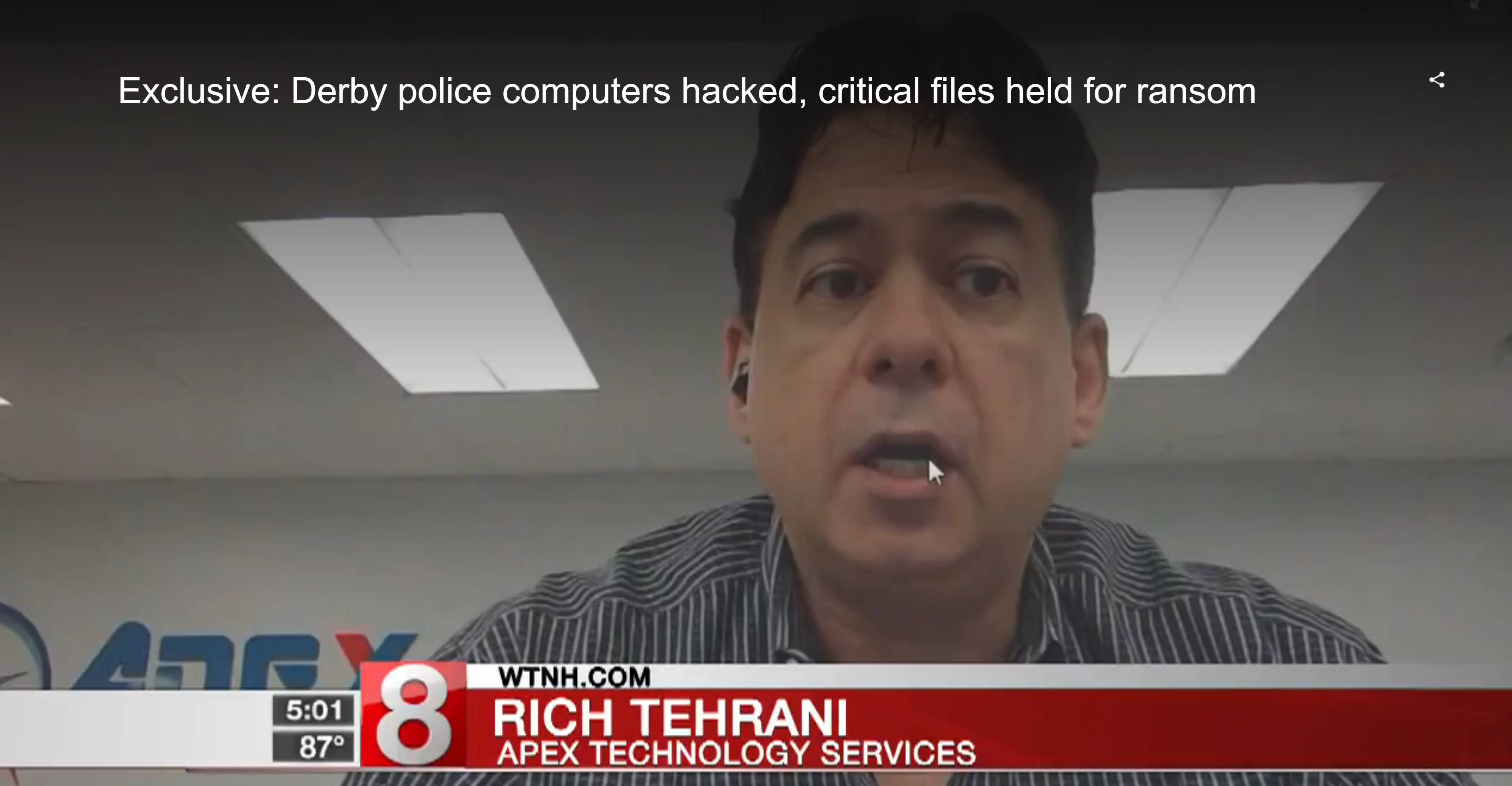
WTNH News recently aired a story on this hack and we were thrilled to be the cybersecurity experts called upon to aid the story. The bottom line is companies need to have a solid backup plan in place to ensure they are cybersecure.
They also need to do the following:
1. Cybersecurity training should be performed every six months. It should ideally be live and interactive. Human error is one of the greatest risks to customer data.
2. Auditing and documentation must be performed regularly to ensure systems are secure. This should be done by personnel who don't run the day-to-day operations.
3. Anomaly detection should be running constantly to detect threats as they emerge.
4. Penetration testing (pen testing) shows if systems can easily be reached and breached. Annual or more frequent pen testing is optimal.
5. An action plan to follow if a breach does occur. Once it happens, few will have the clear heads needed to “wing it” correctly. Equifax botched its response in what is being called a PR catastrophe.
There has been a tremendous increase in cybersecurity incidents. In addition to individual hackers and organized crime syndicates, terrorist groups like ISIS and nation-states like Iran, Russia and North Korea are targeting U.S. corporations and government agencies.
No company can be complacent about protecting customer data and remain in business as the threat is becoming greater, cybersecurity insurance rates are growing and government fines are increasing. The longer an organization waits to deal with these issues, the more peril they will likely be in.
To ensure your organization is as secure as possible, consider the following APEX Connecticut cybersecurity training program included in its comprehensive cybersecurity solution which is the equivalent of the cybersecurity kit mentioned in the Connecticut Cybersecurity Action Plan.
For more information, check out the Apex Technology Services Cybersecurity for your Business Webinar which will focus on the many options businesses of all sizes should consider to keep themselves operating.
It's a must-attend for business owners, office managers, COOs, CIOs, CSOs and anyone involved in ensuring your company is safe and secure and running.
As we've written before, investments in cybersecurity and business continuity are investments in profits as companies can't make sales or work if systems are down.
Please register for this free webinar now, Tuesday, August 7, 2018 - 11:00am ET/ 8:00am PT, even if you can't make it live – we'll archive it for 12 months so you can watch and share at your leisure.




