
Securing a political campaign is far more challenging than securing most organizations because of the dynamic nature of a campaign – the frequent addition of new staff, lack of fixed infrastructure to secure, and difficulty in hiring quality chief privacy and chief security officers. Couple this with the road-warrior nature of top campaign officials and you have a very challenging environment to secure with limited resources or expertise to do so.
The U.S. ranks fifth in the world in election cybersecurity which is clearly unacceptable. Sweden, Northern Ireland, Germany and Italy are ahead while Switzerland, Scotland and the UK are behind.
We explained in How to Secure the 2020 Election the three areas of concern:
- Disinformation
- Hacking campaign officials
- Vote tampering
This post will focus on the second item, which is likely the biggest challenge a campaign can face.
What specific steps should campaigns take to be secure?
Often, the workers are the holes. John Podesta clicked on a single link and entered information which allowed intruders into his email.
Hackers the world over are aware of this and will likely deploy this strategy with even more zeal in future elections.
How do you minimize such risk?
Ensure all workers change passwords on all their accounts at the start of work.
We must assume personal email accounts will be used for work. We can ask that this does not happen but it likely will so it is important to protect against it. Yahoo suffered a massive password breach of three billion accounts in the past and concealed this information from the public. Using Yahoo as a guide, the potential exists for other providers to have been hit as well. They may not be aware. To be on the safe side, ask that all cloud passwords be reset as soon as workers and volunteers start.
Dark web scan.
Scan all the people in your campaign on the dark web to see what information may be there. Often a past email account or other service can be found. Users often use similar passwords across services – or the same one. If their passwords have been listed, they may be easily hacked.
Information on the dark web such as credentials on adult sites may be used to blackmail people in the campaign. A blackmailed user may hand over sensitive information such as passwords.
China was behind the massive U.S. Office of Personnel Management (OPM) hack of 22.1 personnel records consisting of sexual partners, family members and other intimate details of people’s lives. If a worker in your campaign had their information in this database, beware… It can be used to blackmail them or even as a social engineering guide to hack the worker.
It can also be used for pretexting – made famous in 2006 by H.P. when they hired a private investigator to find leakers to the media. The idea is, with personal information, like mother’s maiden name, a company will allow account access. This method can be used to get to phone records, possibly voicemails and more.
Ask campaign workers to minimize the personal information they share online.
This is a challenge for all campaigns where workers tend to be younger and very active on social. Information regarding personal preferences can be used in social engineering attacks to tempt someone to click on a link in an email. For example, if a person shares, they like Ariana Grande, they can be targeted with a special offer which gives them a free concert ticket. If they click, malware can be installed and eventually a user name and password can be stolen. The hacker can then use this compromised account to target other campaign workers and eventually get very valuable information.
Workers need to be trained to understand that any information on the web, pertaining to them can be used as a way to get them to click on links. They need to be vigilant.
Set up and use a VPN.
To be on the safe side, a VPN should be set up and used whenever possible to minimize the risk of information being compromised in transit. This is a cybersecurity 101 best practice.
What are new threats to be concerned with?
Hackers using ransomware will likely start targeting political campaigns.
Hackers have found cities are vulnerable because they don’t take cybersecurity seriously enough. The City of Baltimore has been somewhat disabled for over a month as a result of a ransomware infection. The City of Atlanta was also hit, costing it millions.
Medical facilities such as hospitals have been hit as well and are prime targets because lives may be at stake which in turn could encourage them to pay the ransom.
Political campaigns are a fantastic hacker target for ransomware because every moment counts. A campaign is alive for a relatively short while. Being incapacitated for days, weeks or months is unacceptable, meaning hackers are likely to get paid.
How can you keep your campaign from being a victim?
All systems need to be patched
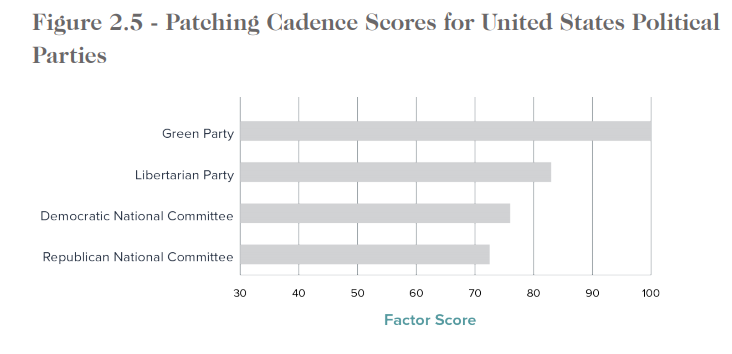
All the computers used in the campaign need to be patched and up to date. Windows 10 for example. The latest browser versions and applications need to be installed. This goes for the hardware as well. The U.S. ranks sixth in the world in patching cadence which is not good.
The extremely virulent BlueKeep for example can infect nearly one million machines around the time of this writing – even after numerous warnings to update have been given to the public from Tehrani.com, Microsoft and the NSA.
It is not uncommon for companies to think they are totally secure because they work in the cloud, yet their firewall or router hasn’t been patched in many years, potentially allowing hackers into the network.
Consumer routers have been shown to have flaws. Keep this in mind when setting up the network.
Have a campaign continuity plan.
Plan for an outage – it could in the form of a hack, weather, flood or service disruption of some kind. If there is a ransomware issue, having solid backups will help! These backups need to be set up professionally with snapshots by day, week, month, etc. They also need to be onsite and in the cloud.
Why? We have seen a restore from cloud taking weeks or more thanks to the sheer volume of information which needs restoring. With a local copy, a machine can be wiped, and restored relatively quickly.
Regularly use a security awareness training solution.
Targeting humans with enticing but malicious messages has become very easy so you must use a service to train users on how to avoid them. Use Phish360 or another service to send fake phishing emails and train users who click.
General Cybersecurity training must be done regularly.
The best way is live or teleconferenced, interactive classroom type education. There is NO substitute for this. Videos are often ignored and webinars may be as well.
Auditing and documentation must be performed to ensure systems are secure.
Think of this as a network inspection. Hackers are continuously probing networks to get in. Organizations must do the same and lock the doors before a hacker goes through one. Ideally a second IT team or MSP/MSSP will check out what another team built.
Anomaly detection should be running constantly to detect threats as they emerge.
Every network is complex and dynamic – changes in behavior such as large file transfers outside of normal hours to suspicious areas such as Eastern Europe, North Korea, Iran or China can be red flags and must be dealt with rapidly.
Penetration testing shows if systems can easily be reached from the outside.
Hackers are constantly probing the entire internet – looking for systems who have misconfigured firewalls and other equipment. The first thing a hacker looking to get in might do is to probe your network for weaknesses.
Hire the best IT services/cybersecurity company you can find.
Political campaigns are massive targets and without professional help, they are sitting ducks. Even if you have internal IT and cybersecurity, outside experts who consult are exposed to new best practices continually. They typically have so many customers that they see new threats earlier than any single company can. Trust in a second opinion to stay secure.
Cybersecurity is a cultural issue
The entire organization must understand they are part of the solution to preventing hackers from getting into a company’s network and shutting it down or stealing information. Without teamwork – there will be holes which could be exploited by an attacker
The author, Rich Tehrani has been recognized as number 8 in the cybersecurity Power 100 and is CEO of Apex Technology Services, awarded Top 10 Network Security Provider. This article contains best practices from extensive experience and from FINRA, NIST, FCC, the FBI, New York (NYCRR 500) and the Connecticut (Cybersecurity Plan).
Please contact us for assistance.



