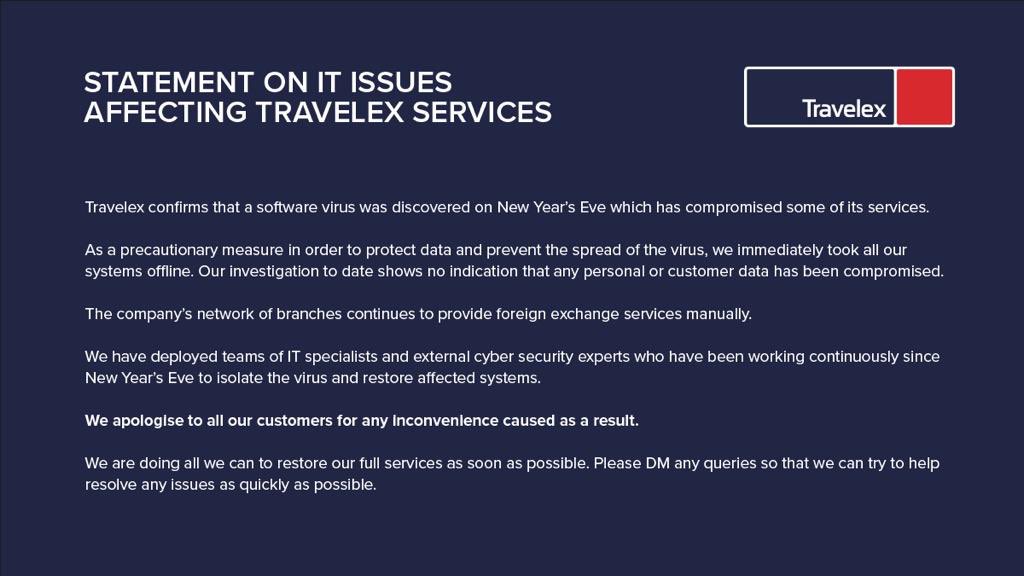
On New Year’s Eve, money transfer and electronic funds company Travelex was hit with a virus shutting down some of its services.
The London-based company, which operates more than 1,500 stores globally, said it took systems offline “as a precautionary measure in order to protect data” and to stop the spread of the malware.
@TravelexUK your uk site doesn’t seem to be working - keep on getting this error on different devices pic.twitter.com/RdBdJxKsd5
— Izzy Fergus (@izzyferg) January 2, 2020
Its U.K. website is currently offline, displaying a “server error” page. Its corporate site said the site was offline while it makes “upgrades.” According to a tweet, Travelex said staff are “unable to perform transactions on the website or through the app.” Some stores are said to be manually processing customer requests.
This news although sad, is common. Recently, New Orleans was hit with Ransomware causing at least a one-million dollar loss and a state of emergency to be declared.
Great Plains Health was hit with ransomware in November, Livingston Schools in new Jersey, were hit in the same month. Finally, around the same time, Petroleos Mexicanos or PeMex for short was hit with ransomware asking for $5 million.
The scary thing to keep in mind is the Americas have become a major target of hacks. 42% of attacks are now aimed here – up from 27% in Q2.
In our experience – when making IT decisions, corporate leaders and boards are still not taking the threat seriously enough meaning they remain vulnerable to paying ransomware ransoms.
Sadly, paying a ransom does NOT mean you will get your data back.
Travelex has not disclosed the type of virus – it is likely ransomware based on what we know so far. Specifically, the company said it took systems offline to “avoid the spread of the malware.” This is basically how ransomware works meaning we feel comfortable saying this is the culprit.
Could this have been prevented?
Possibly. If you want to stay secure, follow these three steps to start:
1) Read cybersecurity essentials – a simple list which will help most organizations become far more secure.
2) Go to a phishing simulation vendor now and sign up for one of their offerings. Phish360 is great and costs nothing to get started. This is needed to train workers by testing them without their knowledge by sending real-looking emails to their inboxes. If they click, they are immediately trained on what not to do.
3) We also recommend you get a free evaluation of your cybersecurity risk from an MSP/MSSP immediately – they can also help you build in the needed compliance to reduce the risk of being fined.



