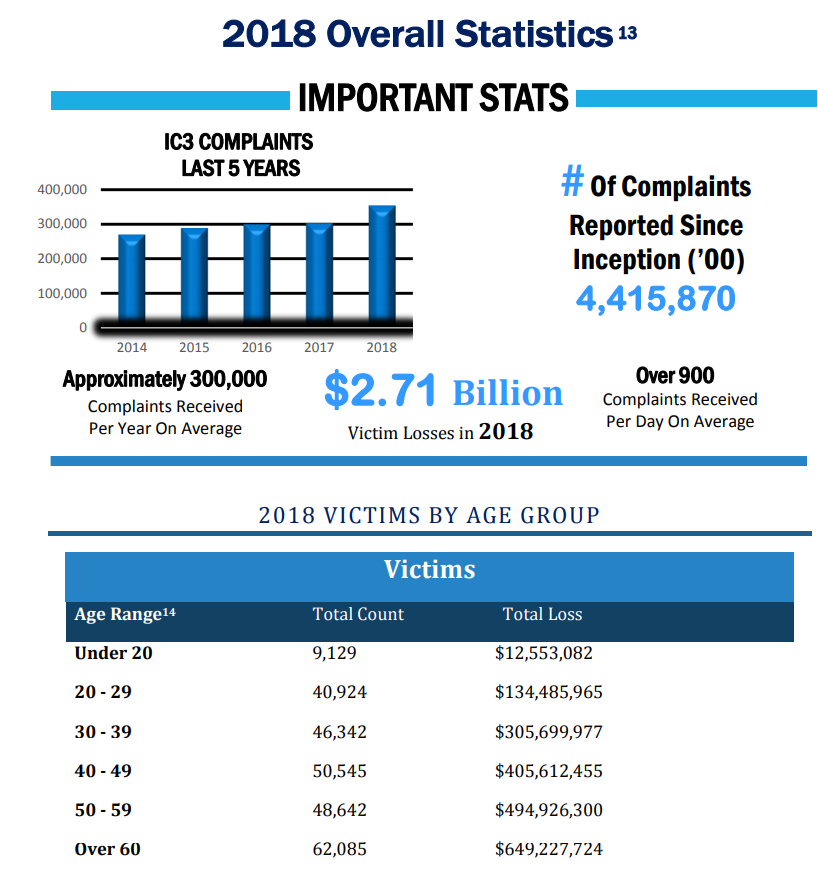
The statistics gathered by the FBI’s Internet Crime Complaint Center (IC3) for 2018 show Internet-enabled theft, fraud, and exploitation remain pervasive and were responsible for a staggering $2.7 billion in financial losses in 2018!
Sadly, things are getting worse.
We’ve recently warned readers that 2019 will be one for the record books when it comes to cybersecurity and sadly our prediction was spot on.
Since our prediction, we’ve had an insider threat in Baltimore, learned half of companies aren’t aware of their IoT breaches, the government shutdown in the U.S. might increase spear phishing attacks, the education market is seeing cybersecurity threats skyrocket, China is attacking the U.S., our home state of Connecticut had a major breach, DHS says the U.S. is not prepared for current cyber attacks, hackers are threatening users with child porn, industrial systems are being hacked and so on.
But back to 2018.
The FBI reports the IC3 received 351,936 complaints in 2018—an average of more than 900 every day. The most frequently reported complaints were for non-payment/non-delivery scams, extortion, and personal data breaches. The most financially costly complaints involved business email compromise, romance or confidence fraud, and investment scams, which can include Ponzi and pyramid schemes.
The bright spots reported by the IC3 include the establishment in February 2018 of the Recovery Asset Team and its success in recovering funds lost in business email compromise scams. These sophisticated scams involve perpetrators infiltrating businesses’ email accounts and requesting fraudulent wire transfers or gift card purchases.
The Recovery Asset Team has helped streamline communication with financial institutions and assist FBI field offices in the recovery of funds for businesses that report a fraudulent domestic transfer. The team was able to successfully recover more than $192 million in funds—a recovery rate of 75 percent.
One recovery success came in Colorado, where a victim wired $56,179.27 for a home purchase to a thief after receiving a spoofed email request from the lending agent. The Recovery Asset Team worked with the Denver Field Office and the victim’s bank to freeze the funds transfer and return $54,000 of the stolen money.
To improve the chances of a successful recovery, it is imperative that victims contact their bank immediately upon discovering a fraudulent transaction as well as report the crime to the IC3.

In 2018, the IC3 received 20,373 BEC/E-mail Account Compromise (EAC) complaints with adjusted losses of over $1.2 billion. BEC/EAC is a sophisticated scam targeting both businesses and individuals performing wire transfer payments. The scam is frequently carried out when a subject compromises legitimate business e-mail accounts through social engineering or computer intrusion techniques to conduct unauthorized transfers of funds.
BEC and EAC are constantly evolving as scammers become more sophisticated. In 2013, BEC/EAC scams routinely began with the hacking or spoofing of the email accounts of chief executive officers or chief financial officers, and fraudulent emails were sent requesting wire payments be sent to fraudulent locations. Through the years, the scam has seen personal emails compromised, vendor emails compromised, spoofed lawyer email accounts, requests for W-2 information, and the targeting of the real estate sector.
In 2018, the IC3 received an increase in the number of BEC/EAC complaints requesting victims purchase gift cards. The victims received a spoofed email, a spoofed phone call or a spoofed text from a person in authority requesting the victim purchase multiple gift cards for either personal or business reasons.
As you might expect, the northeast was a big target of hackers. In terms of number of victims, California clocked in at 49,031 at first place. New York had 18,124 and ranked 4th. New Jersey had 8,440 and ranked 12th. Mass had 6,173 and ranked 47 and finally, Connecticut had 3,134 and ranked 28.
These rankings are similar to the population in each state.
When you consider total losses, California takes the highest spot again with $451M in first place. New York is second at $201M, New Jersey is 9th at $80M, Mass is 10th at $68M and Connecticut is 18th at $38M.
In other words, the companies and people have more money to lose are giving up more assets on a per capita basis.
Every Business must take actions to protect itself. The U.S. Department of Homeland Security explicitly tells us that we are NOT prepared for today’s attacks.
Organizations can choose to be low-hanging fruit, making it easy for hackers to focus on them or do things properly to fend off attackers.
Prevention is crucial. Every company must take these steps:
- Cybersecurity training must be done regularly.
- Auditing and documentation must be performed regularly to ensure systems are secure.
- Anomaly detection should be running constantly to detect threats as they emerge.
- Penetration testing shows if systems can easily be reached from the outside. Here is a case where this test might have saved two company’s’ reputations from being destroyed.
- Network forensics for when a breach eventually occurs. The bad guys always seem to get in eventually.
- An action plan to follow when a breach does occur. Once it happens, few will have the clear heads needed to “wing it” correctly. Equifax botched it’s response in what is being called a PR catastrophe.
- Use phishing simulation which tests employees by sending safe phishing emails. Employees who click are quickly trained on what to avoid.
Protect your organization – even if you have internal IT, hire an experienced MSP or MSSP.
If you do get infected, be sure to hire an MSP with forensic experience who can handle the problem and get you back and running as soon as possible.



