
Ecommerce sites running Wordpress need to be very careful as these sites are huge targets for credit card theft – often using plugins which may not have been patched or via zero-day exploits. Research on a WooCommerce plugin found a script that fetches a favicon file from a hacker’s site. Favicons are the small graphics often shown in web browser tabs.
Photos have a great deal of data associated with them called metadata. You can see what data photos and graphics contain by using a metadata viewer such as metapicz.
The hacker’s favicon looks like the legitimate favicon it replaces but, it has stored a web skimmer in the Copyright field.
The code grabs the input fields from shoppers – credit card numbers, address, etc.
Then an HTTP POST request is used to store the information to the server.
The bottom line here is, the attack is designed to look like normal web activity.
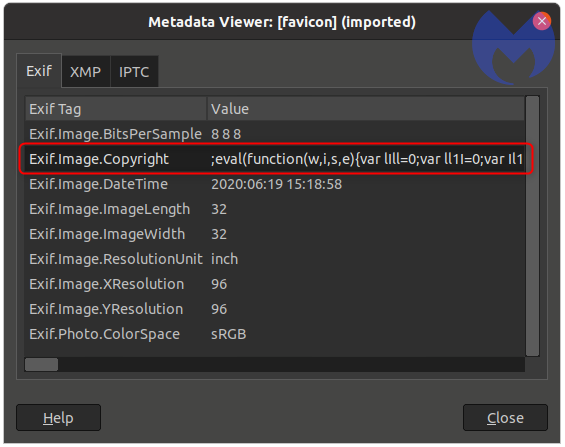
Anomaly detection programs would have a heck of a time figuring out something is wrong.
In fact, it would be tough for anyone using traditional methods to realize this hack was taking place.
We would consider this an esoteric type of attack for these reasons but we only call it that because there aren’t many reported cases of this type of attack as of yet.
What this shows us is hackers are very smart and always evolving.
Cybersecurity involves thinking like the hacker and defending as such.
Patching all your systems as fast as possible is a must.
We further suggest our PHISH360 which is free to use for small businesses – it teaches your team to avoid clicking on malicious email – the most common way hackers get in.
Our company, Apex Technology Services offers cybersecurity assessments which should be done regularly to ensure systems are as secure as possible.
Reference: Malwarebytes Labs, Latest Hacking new



