Hey New York, Is it safe to Use Subway WiFi? Probably Not
Hey New York, Is it safe to Use Subway WiFi? Probably Not
Read MoreRomney, Napolitano Express Concern About Cybersecurity in NYC Homeland Security Hearing
Romney, Napolitano Express Concern About Cybersecurity in NYC Homeland Security Hearing
Read MoreCongressman Says New York Cyberattacks Are Like Pre-9/11 Warnings We Ignored
Congressman Says New York Cyberattacks Are Like Pre-9/11 Warnings We Ignored
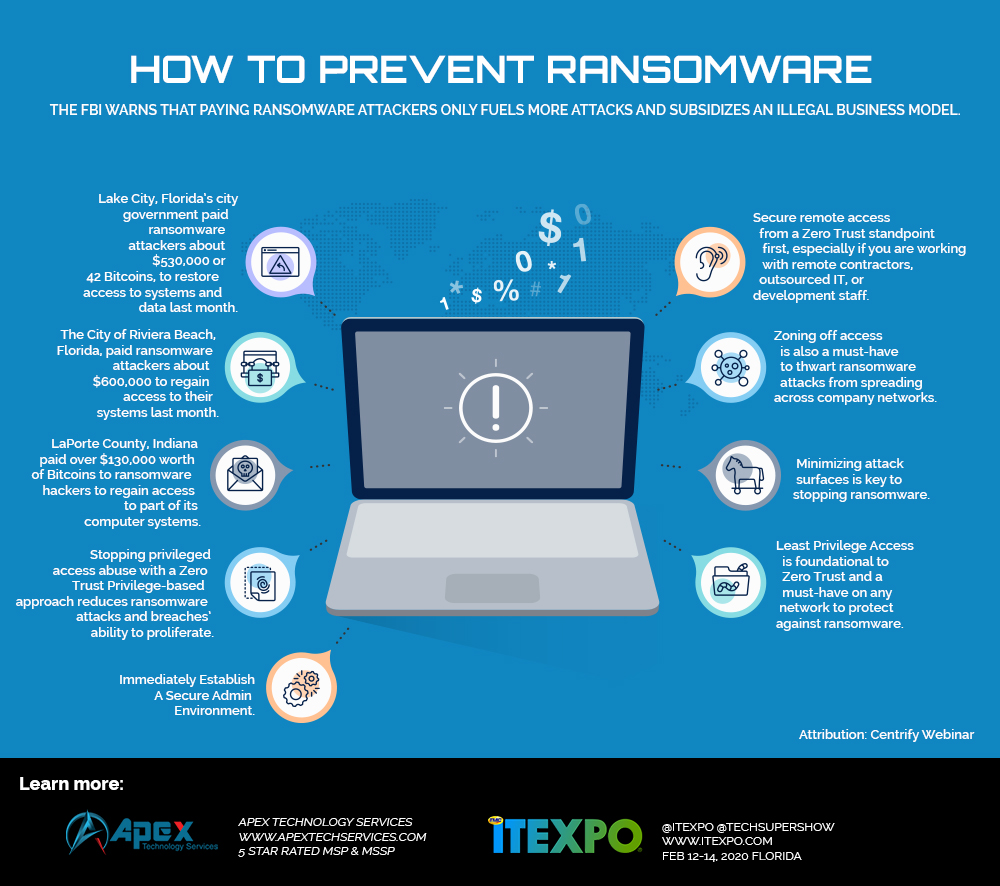
Read MoreHomeland Security Warns Companies About Ransomware
Homeland Security Warns Companies About Ransomware
Read MoreSchools, Government, Healthcare Under Cyber Attack by China and Others
Schools, Government, Healthcare Under Cyber Attack by China and Others
Read MoreWhile we Reported on Ransomware Horrors - Yet Another Was Attacked!
While we Reported on Ransomware Horrors - Yet Another Was Attacked!
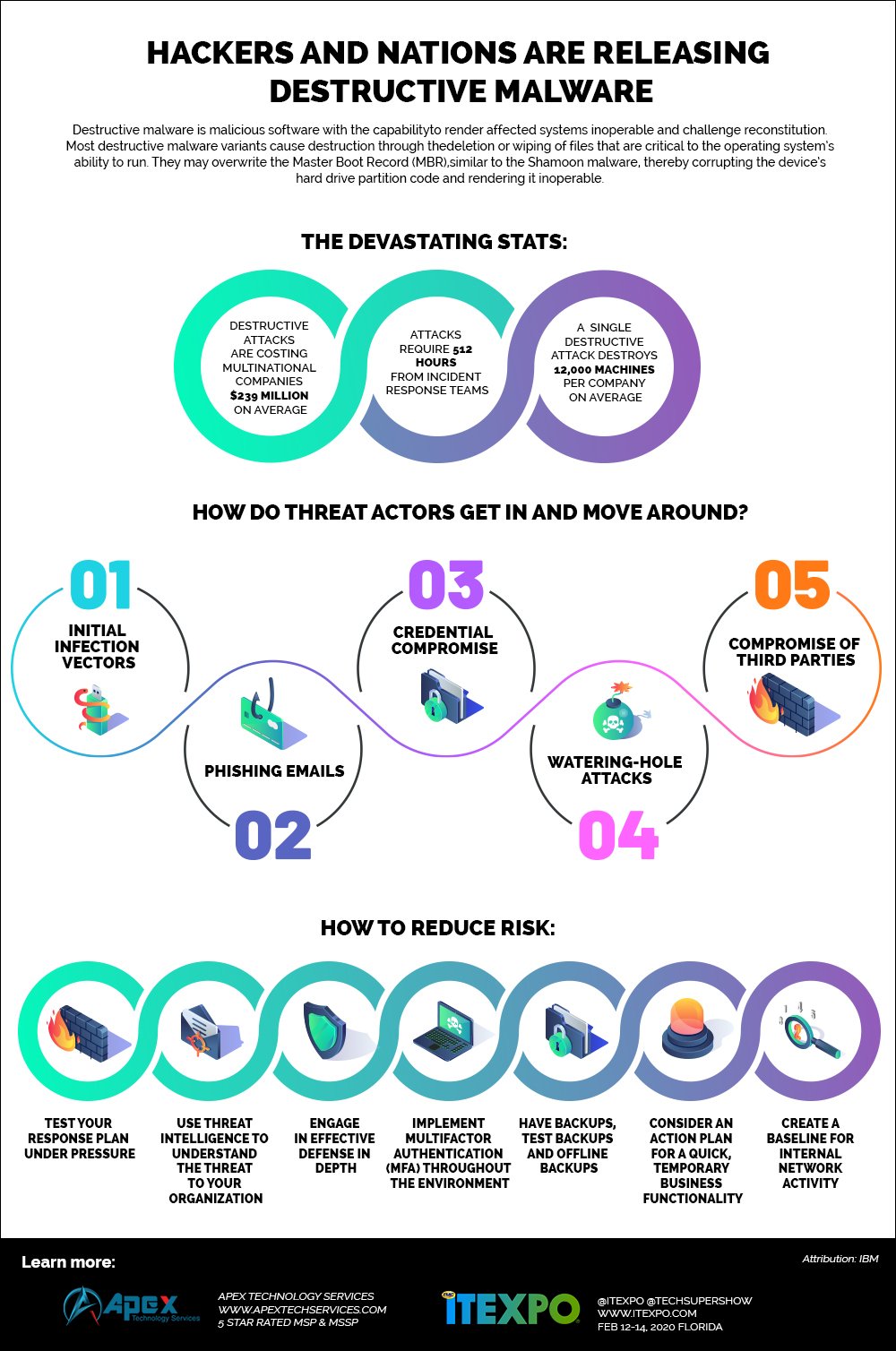
Read MoreHackers and Nations Are Releasing Destructive Malware [Infographic]
Hackers and Nations Are Releasing Destructive Malware [Infographic]
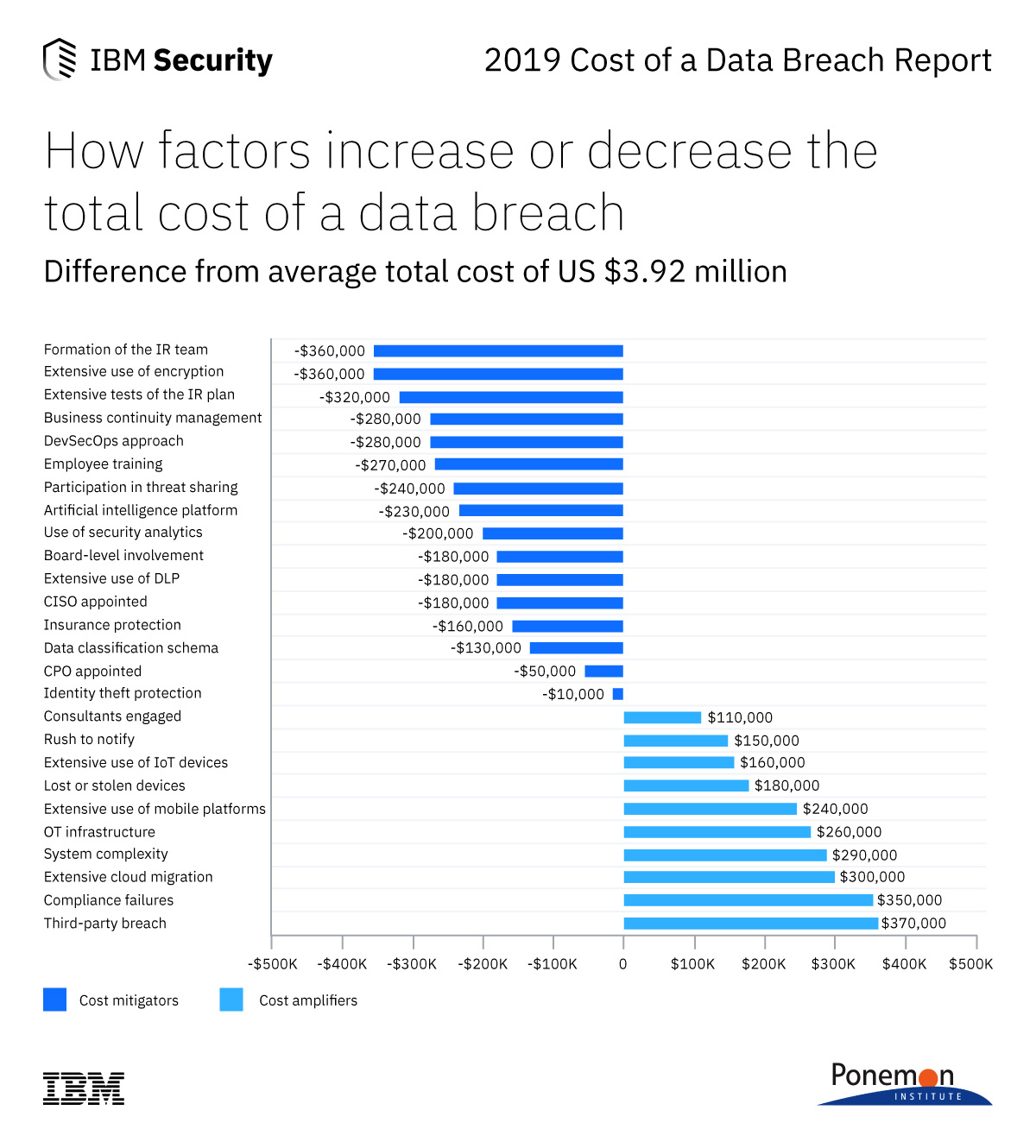
Read MoreProtect Your Company Against The New York Shield Act and Save $250,000
Protect Your Company Against The New York Shield Act and Save $250,000
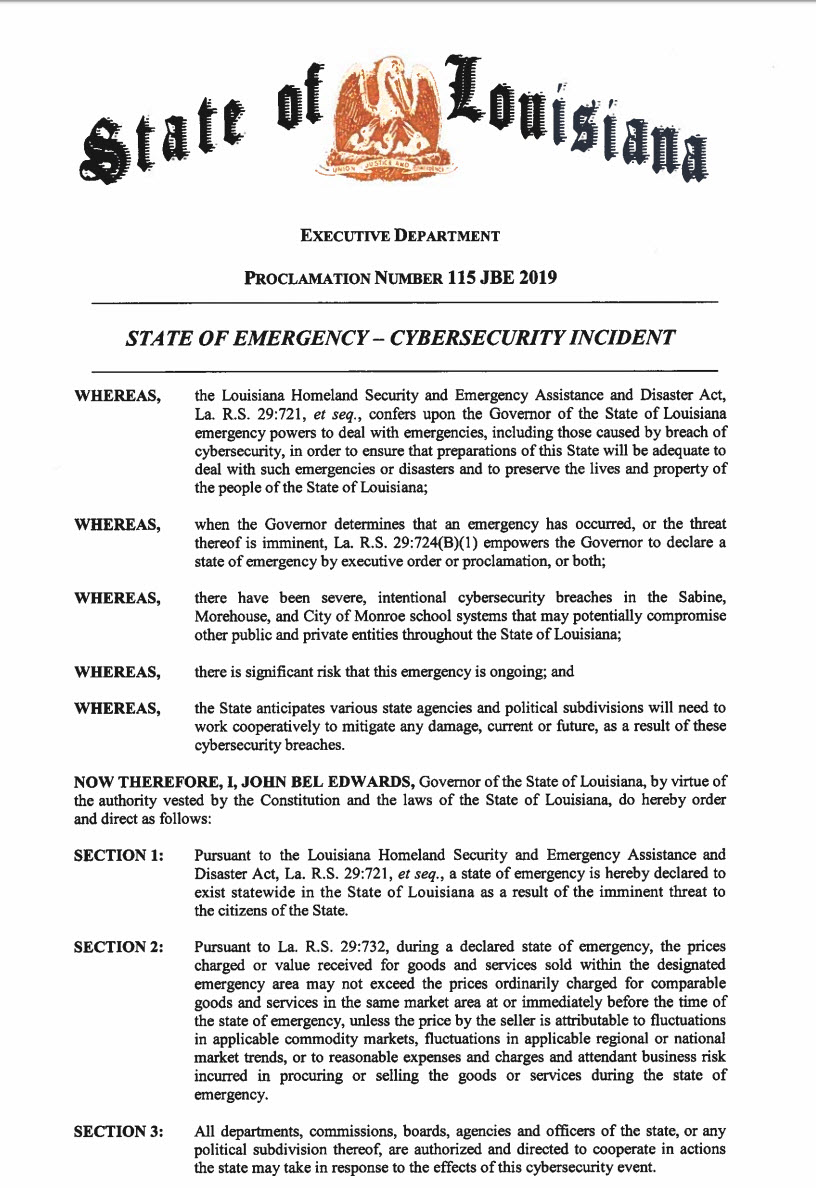
Read MoreRansomware Causes State Emergency in Louisiana
Ransomware Causes State Emergency in Louisiana
Read MoreSmall Business Data Breaches Cost $2.5M on Average!
Small Business Data Breaches Cost $2.5M on Average!
Read MoreReport: State Election Cybersecurity is a Mess
Report: State Election Cybersecurity is a Mess
Read MoreMonroe College Hit With Ransomware and it's Bad!
Monroe College Hit With Ransomware and it's Bad!
Read MoreGDPR Pain! Marriott Fined $123M, UK has Fined $350M in 2 days!
GDPR Pain! Marriott Fined $123M, UK has Fined $350M in 2 days!
Read MoreBritish Airlines is Facing $229M Fine - Could This Happen to Your Company?
British Airlines is Facing $229M Fine - Could This Happen to Your Company?
Read MoreGovernment Warning: Iranian APT33 Hackers Are Targeting the U.S.
Government Warning: Iranian APT33 Hackers Are Targeting the U.S.
Read MoreHuge New Iranian Cyber Threat to U.S. Companies
Russia and Now Iran Cyber War; Companies are on the Front Line
Read MoreBreaches Cost The U.S. $1.6+ Trillion! These Tips Could Keep You Safe
Breaches Cost The U.S. $1.6+ Trillion! These Tips Could Keep You Safe
Read MoreWhat Business Can Learn From This Darien, Connecticut Police Warning
What Business Can Learn From This Darien, Connecticut Police Warning
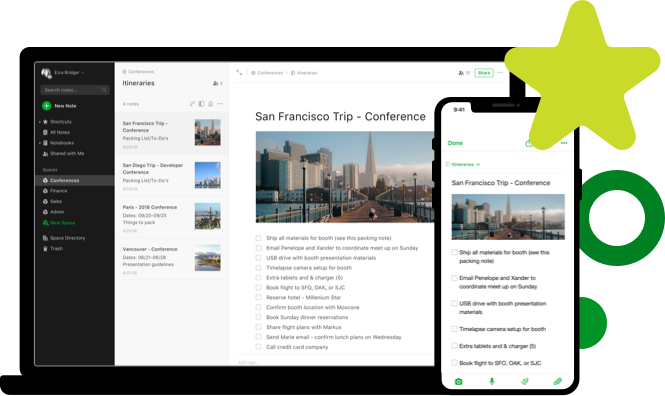
Read MoreEvernote Flaw is a Social Engineering Goldmine
Evernote Flaw is a Social Engineering Goldmine
Read MoreBaltimore is Losing Millions to Ransomware, Your Business Can't Afford to
Baltimore is Losing Millions to Ransomware, Your Business Can't Afford to
Read MoreFirst Coordinated HIPAA Lawsuit Yields $900K Fine
First Coordinated HIPAA Lawsuit Yields $900K Fine
Read MoreCheckers PoS System Hacked, Credit Card Info Stolen
Checkers PoS System Hacked, Credit Card Info Stolen
Read MoreEquifax Breach Cost $1.4 Billion! Caused Moody's Downgrade
Equifax's Cybersecurity Issues Caused Moody's Downgrade
Read More